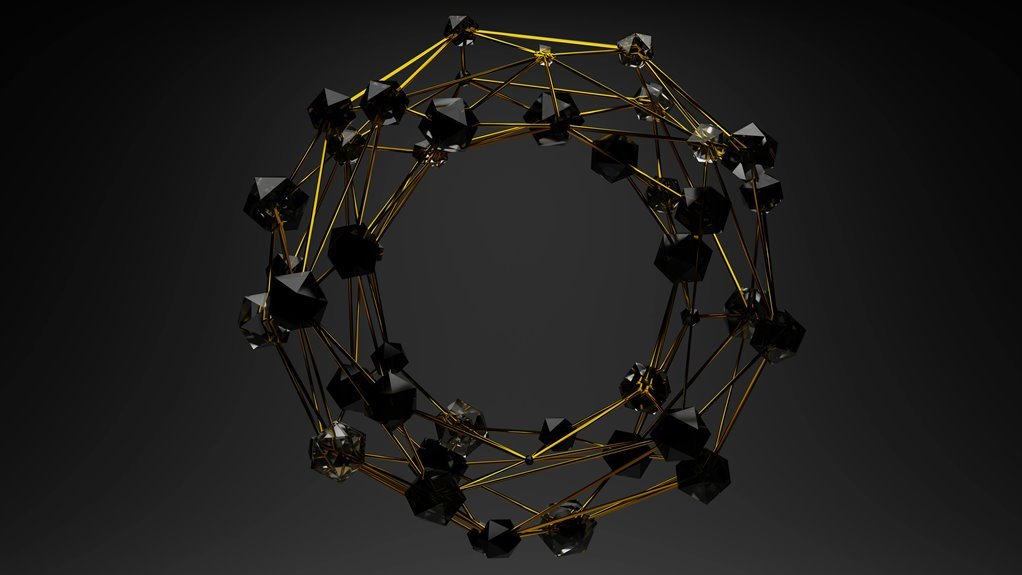
Cyber Node 935950540 Digital Prism represents a modular, high-security data processing unit for aggregating and relaying signals across networks. Its design emphasizes edge analytics, policy-driven filtering, and privacy-aware telemetry. The architecture supports scalable, real-time insights while balancing decentralization with governance. Trade-offs in latency, trust, and data sovereignty challenge traditional models. As networks evolve, questions emerge about governance, interoperability, and the practical limits of edge visibility that demand careful consideration.
What Cyber Node 935950540 Digital Prism Is and Why It Matters
Stated succinctly, the Cyber Node 935950540 Digital Prism is a modular, high-security data processing and monitoring unit designed to aggregate, analyze, and relay digital signals across networked environments. It enables edge analytics, supports data sovereignty, and prompts privacy trade offs.
Its architecture sustains scalable monitoring, offers real time insights, and informs evolving trust models, fostering vigilant, freedom‑minded interoperability.
How Its Architecture Enables Edge Visibility at Scale
The architecture enables edge visibility at scale by distributing data processing and monitoring functions across modular nodes, each equipped with lightweight analytics, secure telemetry, and policy-driven filtering.
Its scale architecture balances decentralization with centralized governance, enabling real world use cases while preserving privacy latency.
Trade offs emerge, from trust considerations to performance, shaping digital prism innovation and edge visibility outcomes across diverse environments.
Privacy, Latency, and Trust: The Trade-Offs in Practice
Privacy, latency, and trust emerge as interdependent constraints in practice, shaping how Cyber Node 935950540 Digital Prism negotiates actionable visibility with respect for user privacy.
The analysis highlights privacy tradeoffs, balancing data minimization with utility, and latency considerations that affect responsiveness.
Trust dynamics hinge on verifiable privacy guarantees, transparent governance, and consistent policy enforcement, enabling users to approve or contest visibility with informed autonomy.
Real-World Use Cases Driving Digital Prism Innovation
Real-world deployments of Digital Prism illuminate how privacy-aware visibility can be operationalized across diverse domains, from enterprise threat monitoring to supply-chain risk assessment.
In practice, data governance frameworks enable compliant data sharing while preserving confidentiality. Anomaly detection systems identify deviations without exposing sensitive details, guiding proactive responses. The approach balances transparency with control, sustaining trust and accountability amid rapid threat evolution.
Conclusion
Cyber Node 935950540 Digital Prism stands as a vigilant conduit between dispersed data streams and centralized governance. Its architecture choreographs edge visibility with disciplined telemetry, delivering real-time insights while respecting policy-driven constraints. Trade-offs between privacy, latency, and trust are managed through adaptive filters and modular scrutiny, ensuring scalable precision without overreach. In practice, it acts as a translucent lattice—ambitious, protective, and ever-watchful—balancing decentralization with accountability to illuminate secure, compliant data pathways.